Provisioning involves mapping users to content and is the aggregation of permissions across three different groupings of users: Domains, Roles, and Users.
- Domain: a specialized group of users in the system which allows for uniqueness;
- Role: an abstract grouping mechanism, geared toward assigning consistent content across Domains;
- User: individual users in the system;
edgeCore ships with one Domain (default), three Roles (All Users, Full Admin, My Domain Admin), and one User (admin).
The user interface lets you shift the unit of focus for the provisioning page via the header dropdown. This enables the administrator to provision content from a variety of different perspectives.
Provision Domains
This screen displays the list of Domains currently configured in the system.
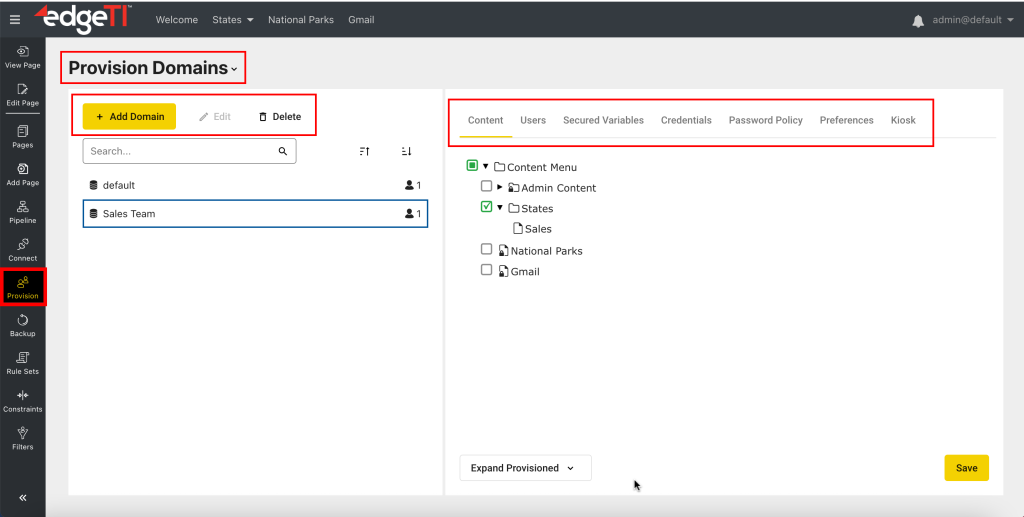
You can modify the list of Domains using the available buttons at the top.
- Add Domain
Used to add a new domain, either embedded (locally managed accounts) or LDAP. - Edit
Used to edit the selected LDAP domain. Embedded domains cannot be edited. - Delete
Used to delete the selected domain from the system. In this case, all users that belong to this domain will be lost. - Filter the list by using the Search field.
Additionally, selecting a Domain on the left provides context to the tabs on the right, enabling you to provision both Content and Users from the perspective of a Domain (see related pages for more information).
Related pages:
– Changing the Default Domain
– Provisioning Content to a Domain
– Managing Users in a Domain
– Configuring Secured Variables
– Configuring Credentials
– Configuring Password Policy
– Configuring Preferences
– Kiosk Mode
Provision Roles
Roles are an abstract grouping of Users and Content and provide a way to provision Content across Domains. For example, an administrator may many want all “Executive” users to get the same set of pages, regardless of what Domain they belong to. This is achieved by:
- Creating an “Executive” Role in the system
- Assigning relevant content to that “Executive” Role
- Giving specific users in the system membership to the “Executive” Role
Multiple Roles can be assigned to users, either directly at the User level, or inherited through a user’s Domain. When a user logs into the system, they do not assume a specific role. The system determines all of the Content assigned to all their Roles, and presents an aggregate view of all of that Content.
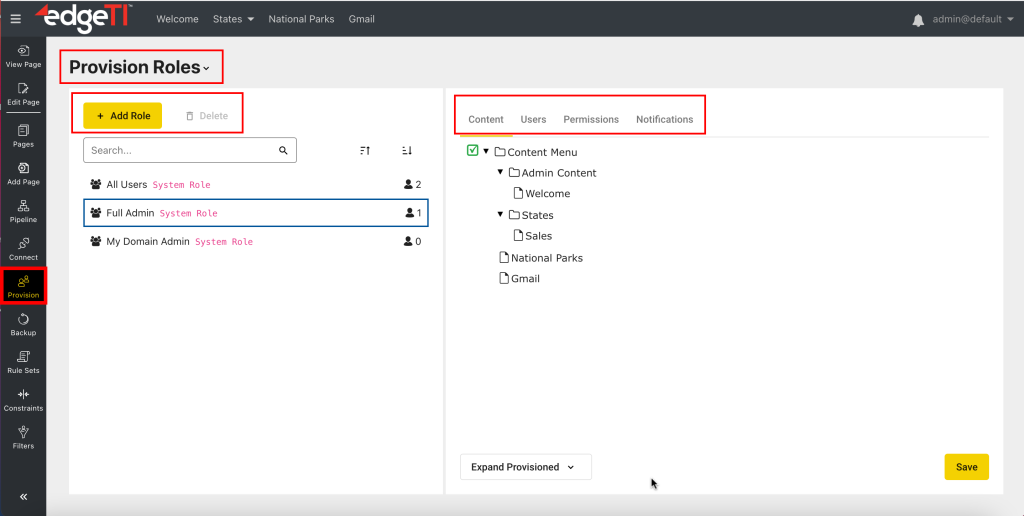
Here you can do the following:
- Add a custom role
- Delete the selected custom role (system roles cannot be deleted)
- Filter the list of roles by using the Search field
- Assign content to the selected role
- Add users to the selected role (or remove them from the role)
- Assign permissions to the selected role
- Define a domain policy
- Assign a notification to the selected role
Provision Users
Users represent the lowest level of provisioning allowed in the system. Provisioning at the User level should be done sparingly because in larger systems it can create a maintenance nightmare. It is considered best practice to provision content using Domains and Roles, and then manage all access to pages by a user’s membership in those Domains and Roles. edgeCore does not permit provisioning of Content directly to Users. If the special case arises that you want to provision Content to a specific individual User, create a Role with only the single User assigned to that Role, and then provision the Content to that Role.
The only restrictions associated with Users are:
- User must belong to a Domain
- User names must be unique within a Domain
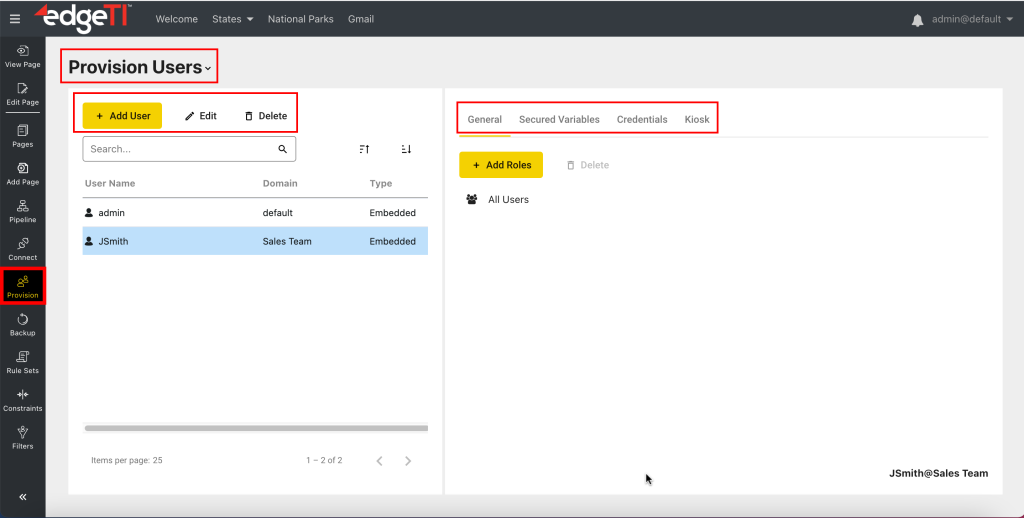
Here you can:
- Add a new user
edgeCore ships with a single user (admin), but you can add an unlimited number of users to the system. - Edit an existing user
- Delete an existing user
- Filter users by using the Search field
- Add roles to the selected user
You can also remove roles from the user. Removing a role from a user does not delete that Role from the system. It only removes an association to the User. The Role will remain. - Assign a specific credential to the selected user
- Add a secured variable to the selected user
Provision Defaults
Defaults represent the concept of “globals” in the system. Administrators can define several different types of defaults, which can be overwritten at the Domain and User level.
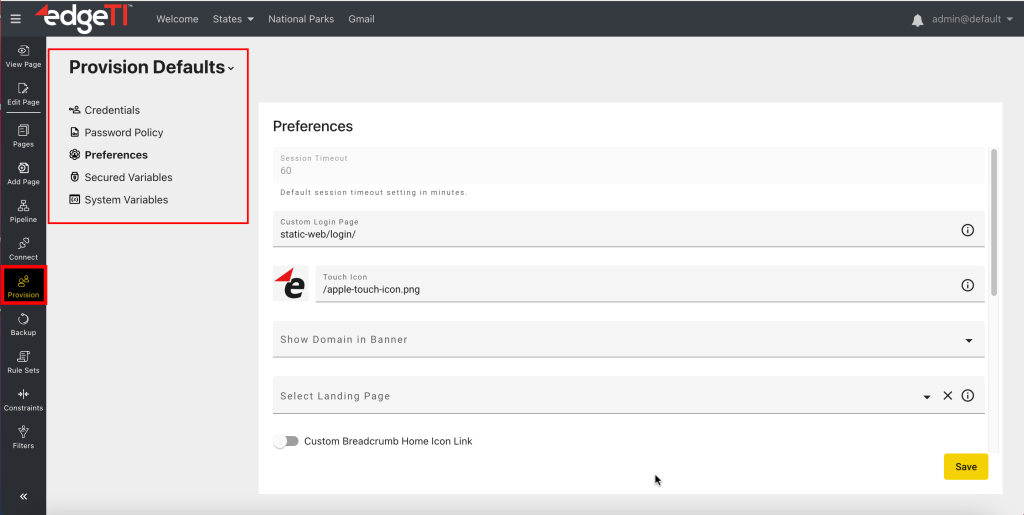
Default Types/Categories are as follows:
- Credentials
Credentials are a specialized grouping of Secured Variables used for authentication. A Credential groups several Secured Variables together so that they can be referenced as a group. An example would be grouping variables “Username” and “Password” together, and then calling that group “Basic Authorization”. - Password Policy
Password policy sets up rules which determine whether or not a password is valid. A password policy can be set up as a system default for all users, or it can target specific groups of users using Domains. - Preferences
Preferences are default values used for specific system settings. These include options for Logo and Theme, displaying a user’s domain name in the banner, setting a landing page, and setting a custom breadcrumb home icon. - Secured Variables
Secured Variables are used to filter data based on values associated with a user’s identity. They are used in queries like Node Variables, but the Secured Variables are evaluated based on provisioning information instead of values in the underlying dataset. Secured Variables can be set for individual Users, or assigned for a group of users using Domains. The other difference from Node Variables is that Secured Variables do not require a default value. So, If no value can be resolved through a default, a Domain, or the User, the data request will fail with an error. - System Variables
Typically used in connections and feeds to help isolate system-specific environment settings. Administrators can set up variants of local.properties for Dev, QA, and Prod systems. They can be used directly when a Connection, Feed, or Transform property supports Expressions, and they can also be used inside of a Secured Variable or Credential when its default value is configured as an Expression rather than a Static Value. There are two types of System Variables: Standard sysVar and Encrypted encSysVar. The first ‘sysVar’ variable type is not encrypted, and the administrator can see the value when inserting it into an Expression. The second ‘encSysVar’ variable type is encrypted. When encrypted encSysVars are accessed, their values in the properties file will be encrypted if necessary. The encSysVar’s value will be displayed as a standard ‘****’ when inserting it into an Expression.